Comprehensive Guide to AUSTRAC Tranche 2 AML Requirements for Individuals and Non-Individuals | Realaml Help Center
Comprehensive Guide to AUSTRAC Tranche 2 AML Requirements for Individuals and Non-Individuals
Complete Guide to AUSTRAC Tranche 2 AML Rules for Individuals & Entities: Stay Compliant with Customer Due Diligence & Reporting Standards.

For Individuals
Identification Requirements
Name:
-
Collect and verify the individual’s full name.
-
Address and Date of Birth:
-
Collect the individual’s residential address.
-
Collect the individual’s date of birth.
-
Verify either the residential address or the date of birth.
-
Name:
Collect and verify the individual’s full name.
Collect and verify the individual’s full name.
Address and Date of Birth:
Collect the individual’s residential address.
Collect the individual’s residential address.
Collect the individual’s date of birth.
Collect the individual’s date of birth.
Verify either the residential address or the date of birth.
Verify either the residential address or the date of birth.
Electronic Verification
For electronic verification, AUSTRAC requires using two reliable and independent data sources. This ensures that information is verified accurately and aligns with Safe Harbour provisions. For example:
-
Name verified against two independent data sources and verification of either date of birth (DOB) or address.
-
Biometric facial recognition checks (e.g., FaceMatch) may also be required to ensure compliance and mitigate fraud risks.
-
For electronic verification, AUSTRAC requires using two reliable and independent data sources. This ensures that information is verified accurately and aligns with Safe Harbour provisions. For example:
Name verified against two independent data sources and verification of either date of birth (DOB) or address.
Name verified against two independent data sources and verification of either date of birth (DOB) or address.
Biometric facial recognition checks (e.g., FaceMatch) may also be required to ensure compliance and mitigate fraud risks.
Biometric facial recognition checks (e.g., FaceMatch) may also be required to ensure compliance and mitigate fraud risks.
Minimum Customer Identification vs. Safe Harbour
Minimum Customer Identification
Involves the collection of basic identifying information for the customer, such as:
-
Full name.
-
Date of birth or residential address.
-
Verification of one of these elements is sufficient.
Used in low-risk scenarios or where simplified due diligence is appropriate.
Involves the collection of basic identifying information for the customer, such as:
Full name.
Full name.
Date of birth or residential address.
Date of birth or residential address.
Verification of one of these elements is sufficient.
Used in low-risk scenarios or where simplified due diligence is appropriate.
Safe Harbour
A stricter process requiring:
-
Two reliable and independent data sources for verification.
-
Verification of both the customer’s full name and either their DOB or residential address.
-
Typically applied to customers in medium-risk scenarios or where Safe Harbour provisions explicitly apply.
A stricter process requiring:
Two reliable and independent data sources for verification.
Two reliable and independent data sources for verification.
Verification of both the customer’s full name and either their DOB or residential address.
Verification of both the customer’s full name and either their DOB or residential address.
Typically applied to customers in medium-risk scenarios or where Safe Harbour provisions explicitly apply.
For Private Companies
Beneficial Ownership
Identify and verify beneficial owners:
-
A beneficial owner is an individual who ultimately owns or controls 25% or more of an entity such as a company, trust, or partnership.
-
Identify and verify beneficial owners:
A beneficial owner is an individual who ultimately owns or controls 25% or more of an entity such as a company, trust, or partnership.
A beneficial owner is an individual who ultimately owns or controls 25% or more of an entity such as a company, trust, or partnership.
Example 1: Identifying Beneficial Ownership by Share Structure
Ash Pty Ltd:
-
1000 shares issued.
-
Mr. Green owns 600 shares (60%), and Mr. Red owns 400 shares (40%).
-
Conclusion: Both Mr. Green and Mr. Red are beneficial owners.
-
Ash Pty Ltd:
1000 shares issued.
1000 shares issued.
Mr. Green owns 600 shares (60%), and Mr. Red owns 400 shares (40%).
Mr. Green owns 600 shares (60%), and Mr. Red owns 400 shares (40%).
Conclusion: Both Mr. Green and Mr. Red are beneficial owners.
Conclusion: Both Mr. Green and Mr. Red are beneficial owners.
Example 2: Voting Rights and Overall Ownership
ABC Pty Ltd Share Structure:
-
Ordinary Shares: 1,000 issued.
-
Preference Shares: 500 issued.
-
ABC Pty Ltd Share Structure:
Ordinary Shares: 1,000 issued.
Ordinary Shares: 1,000 issued.
Preference Shares: 500 issued.
Preference Shares: 500 issued.
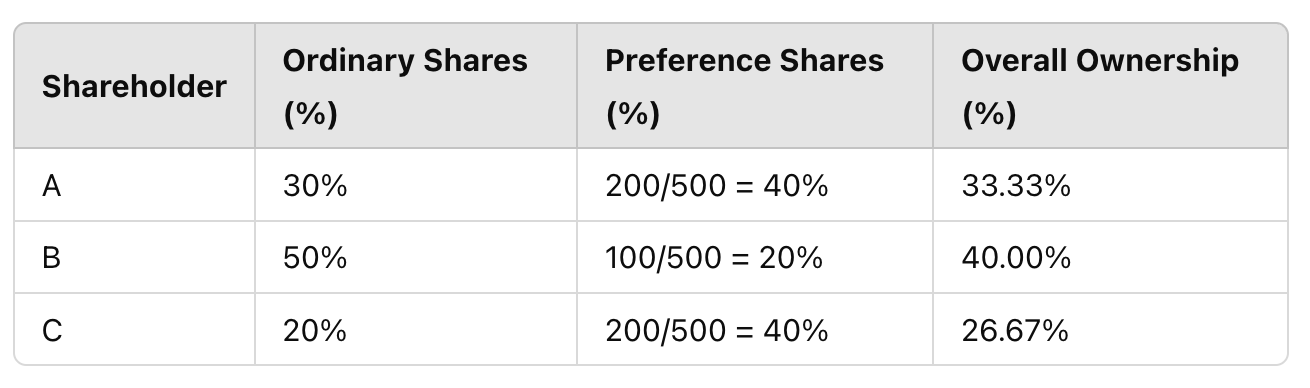
Conclusion: Beneficial owners are those holding 25% or more voting rights or overall ownership, e.g., A, B, and C.
Conclusion: Beneficial owners are those holding 25% or more voting rights or overall ownership, e.g., A, B, and C.
Simplified Verification for Public Companies
Simplified verification applies to:
-
Domestic companies listed on the Australian Stock Exchange.
-
Majority-owned subsidiaries of listed companies.
-
Beneficial ownership identification is not required under these circumstances.
Simplified verification applies to:
Domestic companies listed on the Australian Stock Exchange.
Domestic companies listed on the Australian Stock Exchange.
Majority-owned subsidiaries of listed companies.
Majority-owned subsidiaries of listed companies.
Beneficial ownership identification is not required under these circumstances.
For Trusts
Trustee and Beneficiary Identification
Trustees:
-
Identify and verify all trustees (individual or corporate).
-
For corporate trustees, identify and verify shareholders holding 25% or more.
-
Beneficiaries:
-
Collect the full names of all beneficiaries.
-
Verification may not always be required unless beneficiaries are also trustees or present a higher risk.
-
Trustees:
Identify and verify all trustees (individual or corporate).
Identify and verify all trustees (individual or corporate).
For corporate trustees, identify and verify shareholders holding 25% or more.
For corporate trustees, identify and verify shareholders holding 25% or more.
Beneficiaries:
Collect the full names of all beneficiaries.
Collect the full names of all beneficiaries.
Verification may not always be required unless beneficiaries are also trustees or present a higher risk.
Verification may not always be required unless beneficiaries are also trustees or present a higher risk.
Source of Wealth (SoW) and Source of Funds (SoF)
Collect information on the trust’s Source of Wealth (SoW) and Source of Funds (SoF):
-
Source of Funds: Origin of funds used in the trust (e.g., business proceeds, asset sales, inheritance).
-
Source of Wealth: How the trust’s wealth was accumulated (e.g., investments, property ownership, savings).
-
When Required:
-
High-risk trusts (e.g., involving politically exposed persons or complex structures).
-
Trusts identified in high-risk jurisdictions.
-
Collect information on the trust’s Source of Wealth (SoW) and Source of Funds (SoF):
Source of Funds: Origin of funds used in the trust (e.g., business proceeds, asset sales, inheritance).
Source of Funds: Origin of funds used in the trust (e.g., business proceeds, asset sales, inheritance).
Source of Wealth: How the trust’s wealth was accumulated (e.g., investments, property ownership, savings).
Source of Wealth: How the trust’s wealth was accumulated (e.g., investments, property ownership, savings).
When Required:
High-risk trusts (e.g., involving politically exposed persons or complex structures).
High-risk trusts (e.g., involving politically exposed persons or complex structures).
Trusts identified in high-risk jurisdictions.
Trusts identified in high-risk jurisdictions.
Simplified Verification for Trusts
Trusts are eligible for simplified verification if they meet one of the following:
-
Managed investment scheme registered by ASIC.
-
Unregistered managed investment scheme limited to wholesale clients.
-
Trusts regulated by an Australian Government regulator.
-
Government superannuation funds established under legislation.
-
Beneficial ownership identification is not required for these trusts.
Trusts are eligible for simplified verification if they meet one of the following:
Managed investment scheme registered by ASIC.
Managed investment scheme registered by ASIC.
Unregistered managed investment scheme limited to wholesale clients.
Unregistered managed investment scheme limited to wholesale clients.
Trusts regulated by an Australian Government regulator.
Trusts regulated by an Australian Government regulator.
Government superannuation funds established under legislation.
Government superannuation funds established under legislation.
Beneficial ownership identification is not required for these trusts.
Reliable and Independent Documentation and Electronic Data
AUSTRAC defines reliable and independent sources as those that:
-
Originate from government-issued records, such as passports, driver’s licenses, or birth certificates.
-
Are verified against reputable databases, such as credit reporting agencies or utility company records.
-
Best Practices:
-
Cross-check data against at least two sources to ensure reliability.
-
Ensure data sources are current and not expired.
-
AUSTRAC defines reliable and independent sources as those that:
Originate from government-issued records, such as passports, driver’s licenses, or birth certificates.
Originate from government-issued records, such as passports, driver’s licenses, or birth certificates.
Are verified against reputable databases, such as credit reporting agencies or utility company records.
Are verified against reputable databases, such as credit reporting agencies or utility company records.
Best Practices:
Cross-check data against at least two sources to ensure reliability.
Cross-check data against at least two sources to ensure reliability.
Ensure data sources are current and not expired.
Ensure data sources are current and not expired.
Reference: Reliable and Independent Documentation and Electronic Data
Enhanced Customer Due Diligence (ECDD)
When to Apply:
-
For customers identified as high-risk due to the nature of their business, geographic location, or unusual activity.
-
Examples include politically exposed persons (PEPs) or customers in high-risk jurisdictions.
-
Requirements:
-
Obtain additional information, such as:
-
Purpose of the customer relationship.
-
Source of funds or wealth.
-
-
Conduct ongoing monitoring of the business relationship.
-
Implement stricter controls, such as senior management approval.
-
Reference: Enhanced Customer Due Diligence (ECDD)
When to Apply:
For customers identified as high-risk due to the nature of their business, geographic location, or unusual activity.
For customers identified as high-risk due to the nature of their business, geographic location, or unusual activity.
Examples include politically exposed persons (PEPs) or customers in high-risk jurisdictions.
Examples include politically exposed persons (PEPs) or customers in high-risk jurisdictions.
Requirements:
Obtain additional information, such as:
-
Purpose of the customer relationship.
-
Source of funds or wealth.
Obtain additional information, such as:
Purpose of the customer relationship.
Purpose of the customer relationship.
Source of funds or wealth.
Source of funds or wealth.
Conduct ongoing monitoring of the business relationship.
Conduct ongoing monitoring of the business relationship.
Implement stricter controls, such as senior management approval.
Implement stricter controls, such as senior management approval.
Reference: Enhanced Customer Due Diligence (ECDD)
Realaml’s Enhanced Algorithm
Name Verification:
-
Verify the name against two independent data sources, with additional verification of DOB or address.
-
Biometric Verification:
-
Incorporate FaceMatch for biometric facial recognition to ensure compliance and reduce fraud.
-
Source of Wealth and Source of Funds:
-
Collect and verify SoW and SoF information for applicable trust scenarios.
-
Name Verification:
Verify the name against two independent data sources, with additional verification of DOB or address.
Verify the name against two independent data sources, with additional verification of DOB or address.
Biometric Verification:
Incorporate FaceMatch for biometric facial recognition to ensure compliance and reduce fraud.
Incorporate FaceMatch for biometric facial recognition to ensure compliance and reduce fraud.
Source of Wealth and Source of Funds:
Collect and verify SoW and SoF information for applicable trust scenarios.
Collect and verify SoW and SoF information for applicable trust scenarios.
Key Notes and Recommendations
Electronic Verification Practices:
-
AUSTRAC explicitly requires two independent data sources for Safe Harbour compliance, per its KYC guidance.
-
Industry practices suggest verifying name, address, and DOB using multiple sources to enhance reliability.
-
Resources:
Electronic Verification Practices:
AUSTRAC explicitly requires two independent data sources for Safe Harbour compliance, per its KYC guidance.
AUSTRAC explicitly requires two independent data sources for Safe Harbour compliance, per its KYC guidance.
Industry practices suggest verifying name, address, and DOB using multiple sources to enhance reliability.
Industry practices suggest verifying name, address, and DOB using multiple sources to enhance reliability.
Resources:
Customer Identification and Verification Easy Reference Guide
Know Your Customer (KYC) Requirements
Reliable and Independent Documentation and Electronic Data
Enhanced Customer Due Diligence (ECDD)
This guide aligns with AUSTRAC’s Tranche 2 AML/CTF obligations as outlined in the 2024 Amendment Bill and incorporates best practices for compliance with customer due diligence requirements.
